Analyzing Spear Phishing Email
Phishing is the technique of fraudulent attempt by the attacker to obtain sensitive and confidential information i.e. Credentials, PII information, credit card, bank details. It can also be targeted attack to focus on the specific organization of individual. The attacker often tailors an email to speak directory to targeted user. There are many types of phishing as follow. I wouldn't explain the types. You can read Here. In this article you'll learn how to analyze the sophisticated phishing email. So, Let's start the case study to explain.
Spearphising:
Spearphising is the technique in which attacker aims at one person and lures him/her into providing confidential data. Attacker compile the email according to the specific user. The email would consist some of the target's email, username, designation.
Case Study:
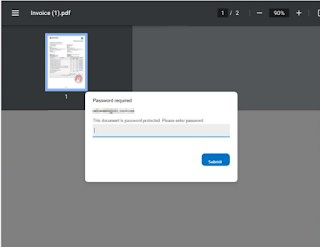
User receive the spearphising email containing the PDF attachment with double extension. Email body contains the unprofessional statement "Kindly make payment for attached invoice immediately to avoid termination". So Let's start the investigation.
Analysis:
Email was pulled from the user's email box to analyze the attachment. Opened the file in editor to view the content of file. Came to know file contains the encoded instruction of HTML and JavaScript which is harvesting the credentials.
 |
| Fig. 2 |
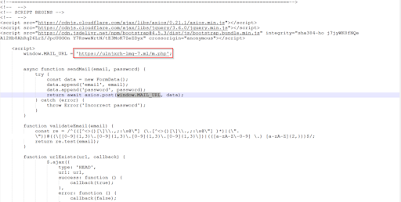
Use the tool "CyberChef" to decode the instructions using recipe "URL Decode" into human readable format.
 |
| Fig. 3 |
Basically threat actor trick the user to provide his email credential which was being sent to actor personal server using HTTP POST request to the URL "hxxps[:]//ulnjxrh-lmg-7[.]ml/m[.]php".
 |
| Fig. 4 |
IOCs:
File Name: invoice-jan-23.pdf.shtml
File Hash: 070650396a8f55391863afc43c1290f60e30425ceadfddb2febeaabba79bd594
Sender Email: erp@erp[.]com
Email Subject: invoice (due)
Domain: hxxps[:]//ulnjxrh-lmg-7[.]ml/m[.]php
Conclusion:
Phishing attacks are becoming a huge problem. Infect, study conducted by PhishMe showed that 91% of cyberattacks started with the phishing email. Organizations should arrange user awareness trainings on regular basis to their employees.

Comments
Post a Comment